Joe Biden and Dilma Rousseff meet at the Palacio do Planalto in Brasilia on June 17, 2014 (Photo: Ricardo Stuckert Filho /PR)
The Obama administration advanced the principle of international openness, accountability and support for human rights this week when Vice President Joe Biden transferred to President Dilma Rousseff a set of newly declassified U.S. government documents relating to Brazil’s military dictatorship, which held power from 1964 – 1985.
Visiting Brazil for the World Cup soccer competition, Biden announced that the Administration would conduct a further review and release of still secret U.S. records to help to the Brazilian Truth Commission; the commission is investigating human rights abuses under military rule and due to issue its final report at the end of 2014. The documentation, Biden stated, would be “of particular interest” to President Rousseff who was a political prisoner and torture victim herself during the military regime. (Diário do Podar, June 17, 2014) “I hope that in taking steps to come to grips with our past we can find a way to focus on the immense promise of the future,” Reuters quoted Biden as saying. (Reuters, June 17, 2014)
Biden’s announcement comes as the U.S. and Brazil are attempting to mend fences in the aftermath of revelations that the National Security Agency had tapped President Rousseff’s cell phone and spied on other Brazilian government agencies.
Peter Kornbluh, who directs the Archive’s Brazil project, commended the Obama administration for the document donation, and hailed the Vice President’s “virtuous use of declassified diplomacy.” According to Kornbluh, “Biden’s diplomatic gesture will not only assist the Truth Commission in shedding light on the dark past of Brazil’s military era, but also create a foundation for a better and more transparent future in U.S.-Brazilian relations.”
The United States covertly supported the military coup that deposed President Joao Goulart on April 1, 1964, and maintained close ties to Brazil’s military rulers during the dictatorship. American diplomats, intelligence operatives and military personnel reported routinely, and in detail, about regime policies – and abuses. The Archive has obtained the release of portions of this critically important historical record through the Freedom of Information Act, and has posted a number of files relating to the U.S. role in the 1964 coup that brought the dictatorship to power.

Dilma Rousseff and Barack Obama at the official launch of the Open Government Partnership in September 2011.
Since the inauguration of the Brazilian Truth Commission in May 2012, the Archive’s Brazil project has been pressing the Obama Administration to conduct a special declassification to assist the Commission’s investigation. With the encouragement of the National Security Archive and others, in recent years U.S. presidents have shared similar records with other governments seeking to recapture their troubled pasts, including in Chile, Guatemala and Ecuador. (See Peter Kornbluh’s recent posting)
Rousseff’s government has been an active proponent of freedom of information. Brazil served as co-chair of the Obama-led Open Government Partnership. In 2012, the country implemented a new information access law, taking a further step out of the persistent shadow of two decades of military rule.
FRINFORMSUM 6/19/2014: The FBI’s Elite Hostage Rescue Team, the Bureau’s 83-Page Guide to Twitter Slang, and Much More.
JUNE 19, 2014
The Pentagon declined to name the units involved in the recent capture of September 11, 2012, Benghazi bombing suspect, Ahmed Abu Khattala, identified by the State Department as a “senior leader” of the Ansar al-Shariah militia. The October 2013 abduction of alleged al-Qaeda operative Nazih Abdul-Hamed al-Ruqai in Libya by Delta Force and members of the FBI’s elite Hostage Rescue Team (HRT), however, likely means that the HRT was involved in the raid to capture Khattala as well. HRT was “a domestic counter-terrorism unit prior to the 9/11 attacks, [which] has become a de facto Special Operations force in its own right.” An earlier Washington Post article revealed more details about HRT’s secret relationship with the Joint Special Operations Command overseas, specifically the bureau’s role in “hundreds of raids” in Iraq and Afghanistan, seen by some as a “natural evolution” for the FBI unit.
As violence in Iraq escalates after the Islamic State in Iraq and the Levant (ISIS) seized the towns of Mosul and Tikrit, the US is being forced to confront its diminished spying capabilities throughout the Middle East. According to reports, a major problem in the wake of the 2011 American troop withdrawal from Iraq is “that much of the intelligence network the U.S. built up during eight years of fighting in Iraq has been dismantled, including a network of CIA and Pentagon sources and an NSA system that U.S. officials said made available the details of every Iraqi insurgent email, text message and phone-location signals in real time.” Lt. Gen Mike Flynn of the Defense Intelligence Agency, however, ‘predicted to Congress in February that the ISIS “probably will attempt to take territory in Iraq and Syria to exhibit its strength in 2014, as demonstrated recently in Ramadi and Fallujah, and the group’s ability to concurrently maintain multiple safe havens in Syria.”’
 The digital library Cryptome recently posted documents on the joint Drug Enforcement Agency (DEA)/National Security Agency (NSA) SANDKEY program, which targets drug trafficking at sea in and around the Caribbean. Considered a successful program, it is largely credited for “the reduced narco-trafficking by boat.” According to Cryptome, the program is administered by the SANDKEY committee, “which includes NSA and DEA, USCG, law enforcement, and the El Paso Intelligence Center (EPIC) which is highly involved. EPIC receives little scrutiny but is a major intelligence player in the central and south Americas and often provides cover for CIA operations.”
The digital library Cryptome recently posted documents on the joint Drug Enforcement Agency (DEA)/National Security Agency (NSA) SANDKEY program, which targets drug trafficking at sea in and around the Caribbean. Considered a successful program, it is largely credited for “the reduced narco-trafficking by boat.” According to Cryptome, the program is administered by the SANDKEY committee, “which includes NSA and DEA, USCG, law enforcement, and the El Paso Intelligence Center (EPIC) which is highly involved. EPIC receives little scrutiny but is a major intelligence player in the central and south Americas and often provides cover for CIA operations.”
Senators Ron Wyden (D-OR), Mark Udall (D-CO), and Rand Paul (R-KY) jointly penned an op-ed for the Los Angeles Times denouncing the intelligence community’s transparency regarding its dragnet surveillance practices, and the watered-down version of the USA Freedom Act recently approved by the House. The Senators were unconvinced that the House version of the bill would end bulk surveillance practices and argued, “This is clearly not the meaningful reform that Americans have demanded, so we will vigorously oppose this bill in its current form and continue to push for real changes to the law.”
While the Senate Intelligence Committee is expected to begin considering cybersecurity legislation that would encourage tech companies “to exchange information on hacking attempts and cybersecurity threats with the government,” those same tech companies are banding together to fight a recent court ruling that would force Microsoft to disclose customer information stored abroad in response to a court-issued search warrant. Microsoft, joined by Verizon, AT&T, Apple, and Cisco Systems, is arguing in court that the US government has “no right” to customer data stored outside the US, and that forcing Microsoft to comply with such an order ‘threatens to rewrite the Constitution’s protections against illegal search and seizure, damage U.S. foreign relations and “reduce the privacy protection of everyone on the planet.”’
A unanimous decision by the U.S. Circuit Court of Appeals for the District of Columbia Circuit will pave the way for a British MP to seek CIA documents on British cooperation with its extraordinary rendition program. The CIA and other intelligence agencies were attempting to deny requests from MP Andrew Tyrie by citing an exemption that prevents intelligence agencies from providing information to “a representative” of a foreign government. The three-judge panel disagreed with the government’s assertions, however, arguing that Tyrie being an elected representative of the British government did not make him its agent, though further noting that “one of FOIA’s traditional exemptions prevents disclosure of classified records, [and] no classified information will see the light of day regardless of how we decide this case.”
An appeals court overturned a lower court ruling this week that would have allowed defense attorneys for Chicago bombing suspect Adel Daoud access to sealed Foreign Intelligence Surveillance Act court records. In its ruling the appeals court argued that the lower-court judge, Sharon J. Coleman, had “disobeyed the statute” by ordering the disclosure of the FISA court records “without first determining whether the surveillance was lawfully authorized.”
More great FOIA work from MuckRock this week spurred the release of the FBI’s official 83-pageguide to twitter and other social media slang, and, more importantly, delved into newly-releasedNSA records management documents. The documents illuminate how long the NSA retains certain documents, and, for the most part, it’s a very short period of time, making records destruction schedules read to some extent “like a guide on how to hide potentially illegal or unethical practices.” The main lesson? Don’t procrastinate sending in your FOIA requests to the NSA, whose SIGINT records are reviewed for destruction every five years, whose employee complaints are destroyed every two years, and whose “weapons and special programs file” is destroyed when no longer needed for operations, however long that may be.
 Of course, NSA records don’t have to be destroyed for the agency to give FOIA requesters the run-around. The NSArecently Glomared (neither confirmed or denied) investigative reporter Jason Leopold’s request for all documents containing the phrases “sniff it all,” “know it all,” “collect it all,” “process it all,” “exploit it all,” and “partner it all,” which were all phrases displayed on an agency slide leaked by former contractor Edward Snowden last year.
Of course, NSA records don’t have to be destroyed for the agency to give FOIA requesters the run-around. The NSArecently Glomared (neither confirmed or denied) investigative reporter Jason Leopold’s request for all documents containing the phrases “sniff it all,” “know it all,” “collect it all,” “process it all,” “exploit it all,” and “partner it all,” which were all phrases displayed on an agency slide leaked by former contractor Edward Snowden last year.
Finally this week, the Archive’s #tbt document pick! This week’s pick is honor of the recent meeting between Brazilian President Dilma Rousseff, one of the fiercest critics of the NSA’s surveillance practices, and Vice President Joe Biden. During the meeting Biden, in response to an Archive initiative and as a gesture of declassification diplomacy, “handed over to Ms. Rousseff declassified documents related to Brazil’s military dictatorship, which seized power in a 1964 coup supported by the United States.” To commemorate the gesture, our #tbt document is a Top Secret March 28, 1964, National Security Council Memcon (memorandum of conversation) discussing how the US ought to support the Brazilian military’s overthrow of populist president Joao Goulart. “The shape of the problem,” according to National Security Advisor McGeorge Bundy, “is such that we should not be worrying that the military will react; we should be worrying that the military will not react.” Read more declassified documents on the 1964 coup here and here.
Happy FOIA-ing!
In response to a lawsuit brought by the Electronic Frontier Foundation (EFF) over its surveillance practices, the National Security Agency (NSA) is arguing that retrieving data collected under Section 702 of the Amendments Act to the Foreign Intelligence Surveillance Act is “too complicated.” NSA Deputy Director Richard Ledgett wrote in a court filing that, “A requirement to preserve all data acquired under section 702 presents significant operational problems, only one of which is that the NSA may have to shut down all systems and databases that contain Section 702 information,” prompting EFF legal director, Cindy Cohn, to say, “it demonstrates that once the government has custody of this information even they can’t keep track of it anymore even for purposes of what they don’t want to destroy.”
The EFF is also asking the Supreme Court to take part in a long-standing FOIA lawsuit in which the EFF is seeking the disclosure of the Department of Justice Office of Legal Counsel (OLC) memo authorizing the FBI to obtain call records without judicial approval. According to EFF Senior Counsel David Sobel, “If the Office of Legal Counsel has interpreted away federal privacy protections in secret, the public absolutely needs access to that analysis. There is no way for the public to intelligently advocate for reforms when we’re intentionally kept in the dark.”
Core transparency concerns have been neglected as Congress argues over definitions of surveillance in the USA Freedom Act. The weakening of the Act in the House, and the current fight over the bill in the Senate, has left the bill stripped of provisions initially intended to be crucial parts of it, including accurate reporting from the Foreign Intelligence Surveillance Court, providing “businesses the ability to release information regarding FISA requests, and creat[ing] an independent constitutional advocate to argue cases before the FISC.”
Microsoft is fighting a federal search warrant seeking information from a customer’s emails stored abroad. Microsoft argued in court that providing the information, currently stored in Dublin, “would violate international law and treaties, and reduce the privacy protection of everyone on the planet.” While the Justice Department argues that a Microsoft victory in the case would be “a dangerous impediment to the ability of law enforcement to gather evidence of criminal activity,” privacy advocates argue that the federal government should pursue other channels for the information, namely cooperative agreements called mutual legal assistance treaties, rather than a search warrant.
For the second year in a row, the Information Security Oversight Office (ISOO) is reporting that the number of reported new secrets is continuing to decline. ISOO also reported that, for the first time in a decade, ‘the number of “derivative classification decisions” in which previously classified information is incorporated into new records also declined.’ ISOO was unable to pinpoint a reason for the decrease, but stated, “possible contributing factors could be the recent emphasis on proper classification procedures coming from the expanded agency self-inspection requirements, the inspector-general reviews conducted in response to the Reducing Over-Classification Act, and the Fundamental Classification Guidance Reviews that all agencies conducted in 2012.”
The Federal Aviation Administration (FAA)announced Tuesday in a landmark decision that it was granting oil giant BP permission to be the first company to begin commercial drone flights over the US. Congress ordered the FAA to provide commercial drones access to US airspace by September 2015, but writing safety regulations for drones 55 pounds and lighter has slowed the agency’s efforts, and the FAA “is not expected to meet the deadline.”
Congressional leaders called the Navy’s latest plan for aircraft carrier-based drones “shortsighted.” Congress is taking issue with the Navy’s relatively conservative plan for its drones; asking contractors for reconnaissance drones that have “only limited ability to carry out bombing missions behind enemy lines.” Congress wants, on the other hand, “cutting-edge warplanes, stealthy drones that can attack key targets in contested areas… [and] could end aviation as the Navy has known it.” Congress halted funding for the Navy’s drone program until the Defense Department can complete a review.
A recent Government Accountability Office (GAO) report shows the Department of Homeland Security (DHS) is continuing to struggle “with planning and prioritizing its strategies,” and has failed to establish “strategic departmental intelligence priorities that can be used to inform annual planning decisions, such as what analytic activities to pursue and the level of investment to make, as called for in DHS guidance.” DHS agreed with both the reports findings and recommendations to fix the issues that were raised.

Abuse allegations prompted CBP to review its use of force. Photo: DON BARTLETTI/LOS ANGELES TIMES — MCT
Abuse allegations and a rise in shooting deaths of unarmed civilians have prompted Customs and Border Protection (CBP), a DHS component, to fire its Internal Affairs director and review its protocol on use of force. This comes on the heels of a McClatchy report that “found that at least 21 civilians have been fatally shot by Border Patrol agents in the past four years, including a 16-year-old who was shot 10 times from behind as he walked along a street on the Mexican side of the border fence that separates Nogales, Arizona, from Nogales, Mexico.”
The House recently adopted an amendment to the FY2015 Commerce, Justice and Science Appropriations bill that will “provide a near-absolute shield for reporters against compulsory disclosure of their confidential sources.” The amendment was introduced by Rep. Alan Grayson (D-FL) and is intended ‘to be construed liberally and broadly, to effectuate its purpose of protecting journalists and their sources from any coercive action taken by the government and the legal system. Its spirit applies to other government agencies, and to litigation between private parties. The terms “information or sources” and “confidential” are to be given the widest possible construction.’
The latest posting from the Archive’s Nuclear Vault includes a newly declassified Sandia National Lab report on the 1961 Goldsboro nuclear accident. The report reveals both that by the time one of the multi-megaton Mk 39 bombs involved in the mishap hit the ground it was in the “armed” setting because of the impact of the crash, and that if the shock had not also damaged the switch contacts, the weapon could have detonated.
Finally this week, today’s #tbt document pick comes from a 2007 posting published to coincide with the auctioning off of macabre memorabilia of Che Guevara’s execution (to lone bidder and Houston bookstore owner, Bill Butler). The document is a June 3, 1975, CIA debriefing of Felix Rodriguez, aka Benton H. Mizones, who was the only CIA operative present at Guevara’s 1967 execution, and the person who informed Guevara he would be killed. After the execution, Rodriguez took Guevara’s Rolex watch and accompanied his body to the airport.

A federal judge in Idaho ruled the NSA program is legal, but should be taken up by the Supreme Court. (Photo: Patrick Semansky/AP/File)
U.S. District Court Judge B. Lynn Winmill upheld the legality of the National Security Agency’s (NSA) bulk collection of American’s phone call data this week. Winmill ruled “binding precedent in the Ninth Circuit holds that call and e-mail metadata is not protected by the Constitution and no warrant is needed to obtain it.” The ruling noted, however, that U.S. District Court Judge Richard Leon’s December ruling that the NSA program likely violates the Fourth Amendment “should serve as a template for a Supreme Court opinion. And it might yet.”
The New York Times recently reported that the NSA is harvesting millions of images from the web for use in its facial recognition programs. According to documents the newspaper obtained from former NSA contractor Edward Snowden, ‘[t]he agency intercepts “millions of images per day” — including about 55,000 “facial recognition quality images.”’ A 2010 document reflected the increasing importance the agency places on digital imagery, noting “[i]t’s not just the traditional communications we’re after: It’s taking a full-arsenal approach that digitally exploits the clues a target leaves behind in their regular activities on the net to compile biographic and biometric information.” NSA chief, Adm. Mike Rogers, responded to the NYT report by saying that the agency is not collecting visual images of people in the US unless they are linked to the investigation of a foreign suspect.
A new Office of Director of National Intelligence directive that requires all employees and contractors to obtain “authorization before disclosing any intelligence-related information to the public” is confusing and frustrating many intelligence agency employees. One –anonymous– former official called the directive both outrageous and ineffective at stopping the next Snowden, while another argued it is an individuals right to talk about intelligence issues so long as no classified information is revealed.
The Supreme Court rejected an appeal from New York Times reporter James Risen over his refusal to testify in a leaks case. At issue is Risen’s refusal to testify in former CIA official Jeffrey Sterling’s leaks trial that resulted from his disclosures regarding Operation Merlin, a Clinton-era CIA effort to sabotage Iranian nuclear research, which was the subject of a chapter in Risen’s 2006 book, State of War. The Obama administration has sent mixed signals about the case, with Attorney General Eric Holder hinting last week that the government might not pursue jailing Risen for his refusal to testify, all the while pursuing the administration’s right to do so.

Sen. Dianne Feinstein released emails between Snowden and NSA’s General Counsel, saying they prove there was no “smoking gun.” Snowden responded saying the emails are deliberately incomplete. Photo: Bill Clark/CQ Roll Call
Senator Dianne Feinstein (D-CA), chair of the Senate Intelligence Committee,released contents of a brief e-mail exchange between Edward Snowden and the NSA’s Office of General Counsel last week. While Feinstein reported that “the NSA informed the committee that it has found no evidence that Snowden expressed concerns or complaints, in email or any other form, about NSA’s intelligence activities to anyone in a position of authority or oversight,” Snowden said the e-mails were incomplete. Snowden told the Washington Post that,“[t]he NSA’s new discovery of written contact between me and its lawyers – after more than a year of denying any such contact existed – raises serious concerns.”
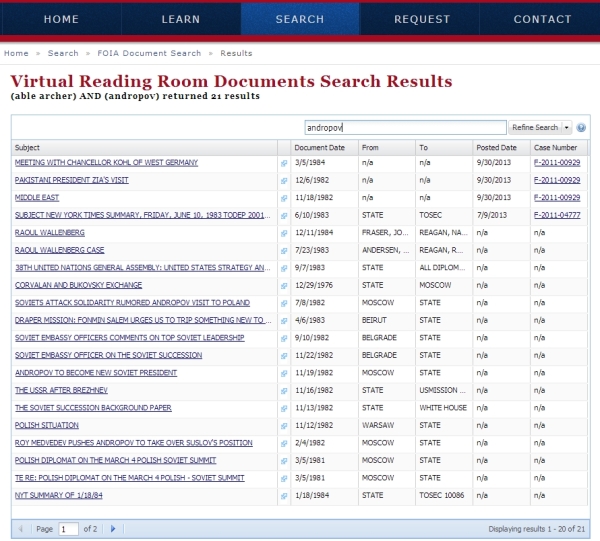
Snowden’s leaks about the NSA’s bulk data collection programs spurred thousands of FOIA requesters to submit records requests to the agency, and documents released to The Guardianshow the agency’s FOIA staff struggled to respond and sought ways to deny releasing records en masse. According to Archive FOIA Coordinator Nate Jones, “[f]or those who believe the public has the right to know what information the NSA is allowed to collect the conclusion drawn in this case is that the Snowden leaks worked and the Freedom of Information Act did not.”
In an unusual move, the International Committee of the Red Cross was not invited to interviewthe five Guantanamo detainees released in the prisoner exchange for Sgt. Bowe Bergdahl. The Obama administration also withheld its statutory 30-day notice of the exchange from members of Congress, only informing Congress about the exchange while it was underway.
Documents released through the FOIA raise the question why the FBI was investigating Michael Hastings’ reporting on Bergdahl? Hastings, who wrote “the definitive first account of Bowe Bergdahl” for Rolling Stone in 2012 –a largely unflattering depiction of the soldier–, died in a car accident in June 2013. After his death, FOIA requests filed by Jason Leopold and Ryan Shapiro to the FBI resulted in the release of heavily redacted FBI document characterizing Hastings’ reporting as “controversial,” and show the bureau extensively investigating the reporting behind the 2012 Rolling Stone article.
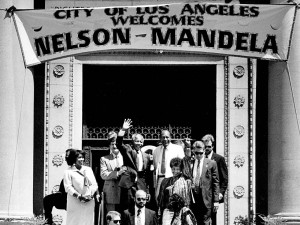
LA Mayor Tom Bradley gave Nelson Mandela meet the key to the city during a June 1990 visit. Photo: the Los Angeles Times.
Documents released to Ryan Shapiro in response to a FOIA lawsuit also reveal that the FBI spied on Nelson Mandela during his first visit to the US in 1990. Mandela was still on the US’ terror watch list at the time of his visit, and his party, the African National Congress, was a designated US’ terrorist organization. Considering that the CIAlikely played a role in Mandela’s 1962 arrest, according to Shapiro, “[w]hat’s missing from these documents is often as illuminative as what’s disclosed. Not only did the FBI heavily redact and withhold documents, but there’s virtually no discussion of U.S. intelligence community involvement prior to Mandela’s 1990 release from prison.”
To commemorate the 25th anniversary of the Chinese government’s vicious crackdown on pro-democracy protestors at Tiananmen Square on June 4, 1989, the National Security Archive published 25 Defense Intelligence Agency (DIA) records, obtained through the FOIA, for the first time. The DIA records address the 1989 protests, which culminated in the June 4 massacre, and a range of other security-related concerns with important implications for the political longevity of the Chinese leadership.
Leading decision makers from the United Nations, Africa, the United States, and Europegathered in the Hague from June 1 to 3 to consider the failure of the international community to prevent or effectively respond to the 1994 genocide in Rwanda. The conference was jointly sponsored by the United States Holocaust Memorial Museum and The Hague Institute for Global Justice, in cooperation with the National Security Archive to mark the 20th anniversary of the genocide. The conference coincided with the release of newly-declassified reporting from 1994 by key members of the UN Security Council, which provides a previously unavailable day-by-day narrative of the international response to the Rwandan genocide. The documents “offer a vivid record of closed-door debates, in which the diplomats, lacking accurate information and scarred by a disastrous military mission in Somalia months earlier, voted to pull out most of the peacekeepers at the very moment that they could have curbed the killing.”
Finally, this week’s #tbt document pick! This week’s selection is a Secret June 14, 1963, memorandum –nearly a year after Nelson Mandela’s arrest–, from U. Alexis Johnson, Deputy Under Secretary for Political Affairs, to Secretary of State Dean Rusk. Johnson says he believes apartheid will eventually prove “disastrous,” but advises against imposing a total arms embargo on South Africa because its cooperation with the U.S. on aircraft landing rights, tracking stations, and ports, will be increasingly important if the U.S. can’t maintain access to the Suez Canal.
Happy FOIA-ing!
With the 25thanniversary of the Tiananmen Square massacre at hand, Chinese authorities have erected “more impact resistant” railings around the square itself, rendered Google “largely inaccessible,”detained lawyers, arrested scholars,disappeared activists, and shamed journalists. This is all ostensibly to suppress debate over the military crackdown of the 1989 pro-democracy protests that resulted in the June 4, 1989, massacre of an unknown number of Tiananmen Square demonstrators. Unsurprisingly, the Chinese narrative on one of the most seminal events in its modern history remains, for the most part, sparse.
Luckily, newly declassified documents released to the National Security Archive by the Defense Intelligence Agency (DIA) will help fill in some of the gaps. The DIA documents support the view that there was only a “limited split” in Chinese leadership on using lethal force against citizens, and shed new light on events during and after the protests, complementing previously declassified US diplomatic cables and CIA reports to do so.
The documents show that by April 19, 1989, as pro-democracy demonstrations were beginning to escalate in Beijing, the DIA was reporting that the Chinese government’s response to student demonstrations was “restrained,” but that further “escalation of student protests will most likely trigger a government crackdown.” Nearly a month later, on May 17, demonstrations had so escalated, and it was reported that an estimated 1 million people were protesting in Beijing. According to DIA analysis, onlookers generally supported the demonstrators and provided them with food and money. The same source indicates that by mid-May soldiers were allegedly already refusing to deploy to Tiananmen Square, and that on May 15 a unit in Boading “failed to deploy” despite Beijing’s orders.
In light of growing demonstrations and evidence that the army might be unwilling to use force against the protesters, on May 19, 1989, the DIA reported that the Chinese Communist Party (CCP) seemed to “have little choice but to make serious concessions to the students.” It also noted that government infighting was sending mixed-messages to both students and the army, and that “several group armies” were being moved to Beijing.

Li Peng, China’s premier, declared martial law on May 20, 1989, in response to growing protests in Tiananmen Square (photo credit: World Economic Forum).
By May 18 or 19, however, CCP General Secretary Zhao Ziyang was the only voice opposing military force against the protesters. Upon realizing his calls for moderation had been ignored, Zhao met with students at Tiananmen on May 19, saying, “We have come too late.” Chinese premier Li Peng declared martial law the following day.
Later DIA analysis, drawn from the 1990 edition of the Directory of the PRC Military Personalities, lists the highest estimates of troops used to suppress the protest after Zhao was outvoted at 350,000 men, including “elements from at least 14 of the PLA’s [People's Liberation Army] total of 24 groups armies (GA’s) and two airborne brigades.”
Chinese leaders tried to promote the appearance of a return to normalcy in the immediate aftermath of the 1989 protests, insisting they were a “counter-revolutionary riot, involving a tiny minority of troublemakers.” The CCP’s security concerns surrounding hosting the 1990 Asian Games, however, belies the portrayal of the protests as a contained riot perpetrated by an unhappy minority. According to a declassified DIA cable, the Chinese government viewed the 1990 Asian Games as “a rite of passage” and as a key point in both the nation’s long-term economic development and returning to “international respectability” after Tiananmen, and a Secret April 16, 1990, report notes heavy security and riot police around Tiananmen Square and the Asian Games stadium in the lead-up to the Games to subdue any potential disruptions. An April 12, 1991, cable further notes that after the Games the PLA generally kept a low profile because the 1989 crackdown “seriously tarnished” its image. In response, the People’s Armed Police force grew to 30,000, and assumed a “greater responsibility for internal security.”
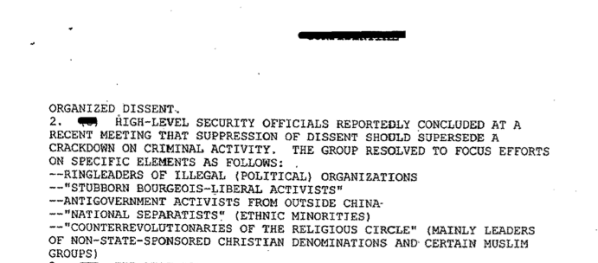
In the years after the 1989 protests, possible June 4 anniversary protests became an annual concern for Chinese leadership, with one May 7, 1990, cable expressing fears that “the situation in China is explosive.” One of the most revealing documents reporting on the Chinese government’s suppression of dissent surrounding the Tiananmen anniversary is a Confidential January 10, 1992, cable. The cable reports that according to a group of Chinese officials, ‘suppression of dissent should supersede a crackdown on criminal activity. The group resolved to focus efforts on specific elements as follows:
- “Stubborn bourgeois – liberal activists”
- Antigovernment activists from outside China
- “National separatists” (Ethnic minorities)
- “Counterrevolutionaries of the religious circle” (mainly leaders of non-state sponsored Christian denominations and certain Muslim groups)’
Taken together, these DIA documents support previous reports that there was only a “limited split” among top Chinese leadership on using force against protesters, but that “both senior officers and rank-and-file soldiers had basic qualms about confronting their fellow citizens with lethal force.” Read in conjunction with diplomatic cables and CIA reports, these DIA documents help provide a more complete picture of the 1989 protests and Tiananmen Square.
Please visit the National Security Archive for more information on Tiananmen Square at 25 years, Tiananmen Square, 1989: The Declassified History, and The U.S. “Tiananmen Papers.”
Hague Conference Examines International Community’s Failure to Prevent Rwandan Genocide
MAY 30, 2014
 Leading decision makers from the United Nations, Africa, the United States, and Europe will gather in The Hague from June 1 to 3 to consider the failure of the international community to prevent or effectively respond to the 1994 genocide in Rwanda and to explore whether and how the tragedy might have been averted.
Leading decision makers from the United Nations, Africa, the United States, and Europe will gather in The Hague from June 1 to 3 to consider the failure of the international community to prevent or effectively respond to the 1994 genocide in Rwanda and to explore whether and how the tragedy might have been averted.
This rare convening of former officials and eyewitnesses, jointly sponsored by the United States Holocaust Memorial Museum and The Hague Institute for Global Justice, in cooperation with the National Security Archive (George Washington University), coincides with the 20th anniversary of the genocide, a deliberate campaign of killing that took the lives of as many as one million Rwandans, predominantly Tutsis, between April and July 1994.
Thousands of pages of newly declassified documents have been made available online by the conveners as part of a broader initiative to shed new light on the failed response to the genocide. Declassification requests that the National Security Archive and the Holocaust Museum made in four countries have resulted, most recently, in the release of nearly 300 formerly secret diplomatic cables that provide fresh insights into closed UN Security Council sessions in the days and weeks leading up to the genocide. These newly released documents, which will be available on the National Security Archive and Holocaust Museum websites starting Monday, June 2, include reporting from key players in the Security Council debates, in addition to previously withheld US diplomatic traffic. They include cables from three officials who will attend the conference: New Zealand envoy Colin Keating, president of the Security Council in April 1994; Sir David Hannay, the British permanent representative to the UN; and Karel Kovanda of the Czech Republic, who was the first UN ambassador to use the term “genocide” to describe the events in Rwanda.
Tom Blanton, director of the Archive, said, “The remarkable new documentation obtained by our project pulls back the curtain over UN deliberations in 1994 and goes right to the question of why and how the international community failed to respond and to protect Rwandans. Now, thanks to the Holocaust Museum and The Hague Institute, this remarkable group of former officials and eyewitnesses is coming together to learn from each other, and from the new evidence, to prevent future catastrophes like Rwanda.”

International Humanitarian Aid, Rwanda, circa September 1994. Photo from personal collection of Prudence Bushnell.
Participants in the conference,International Decision Making in the Age of Genocide: Rwanda 1990-1994, include architects of the 1992-93 Arusha Accords; the leadership of UNAMIR, the UN peacekeeping force in Rwanda; four former members of the UN Security Council; senior officials from the United Nations, Africa, the United States, and Europe; and former diplomats, human rights activists, academics, and journalists present in Kigali before and during the genocide. Lieutenant-General Roméo Dallaire, leader of the ill-fated UN peacekeeping mission in Rwanda and recipient of the 2014 Elie Wiesel Award — the Holocaust Museum’s highest honor — for his bravery and moral courage in helping save some 30,000 lives, will also participate.
The conference is modeled on a series of “critical oral history” gatherings co-organized by the National Security Archive over the past 25 years that have dramatically expanded public and scholarly knowledge of the Cuban Missile Crisis, the Vietnam War, the end of the Cold War, and US-Iran relations, among other topics. This conference will focus on: the lead-up to the genocide between October 1990 and April 1994, asking such questions as whether the international community might have been able to foresee and prevent the gathering catastrophe in Rwanda; the international response to the genocide, with special attention paid to the role of the UN Security Council; and the similarities and differences between Rwanda and other contemporary mass atrocities.
This conference is made possible in part by the generous support of the Sudikoff Family Foundation, which funds the Holocaust Museum’s Sudikoff Annual Interdisciplinary Seminar on Genocide Prevention, and the John D. and Catherine T. MacArthur Foundation, which helps to underwrite the National Security Archive’s genocide documentation efforts.
Please visit the National Security Archive for more information.
Remembering an Archive Hero
MAY 29, 2014
William Worthy, a foreign correspondent who travelled to –and reported from– locations the US government did not want him to go, died this month at the age of 92.
Worthy traveled to places like the Soviet Union, Cuba, and China because he believed Americans “have a right to know what’s going on in the world in their name,” and it would be difficult to exaggerate his contributions both to investigative journalism and the founding of the National Security Archive.
Worthy’s intrepid reporting made him the subject of a landmark federal case concerning travel rights. He is perhaps most famous for his 1961 arrest after returning to the US from Cuba where he interviewed Fidel Castro. Upon return he was arrested, not for illegally traveling to Cuba, but for re-entering the US without a passport, which the State Department had refused to renew years before after he violated a US travel ban and spent 41 days in China. The travel rights case made him the subject of protest singer Phil Ochs’ “The Ballad of William Worthy,” which includes the lyrics: William Worthy isn’t worthy to enter our door./ Went down to Cuba, he’s not American anymore. /But somehow it is strange to hear the State Department say, /You are living in the free world, in the free world you must stay.
Mr. Worthy, albeit somewhat inadvertently, also played a key role in the founding of the National Security Archive in 1985.
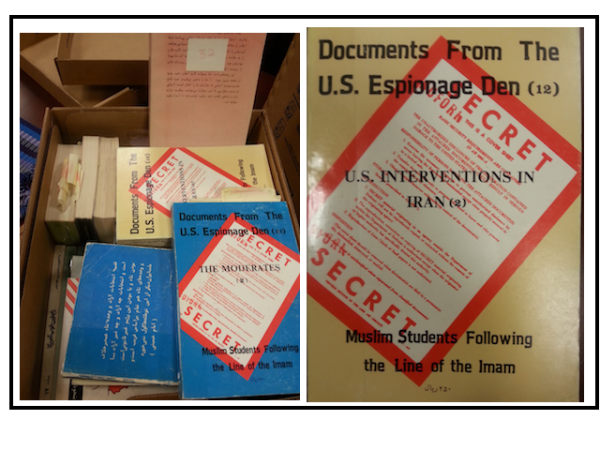
In 1981 Worthy, undeterred by the government’s attempts to prevent him from traveling where they didn’t want him to go, flew to Iran to report on the Islamic revolution as a freelance producer for CBS News. While there, he bought a multivolume set of books that were readily available in Iran and were already circulating through Europe. These volumes were “said to be reprints of intelligence documents taken from the United States Embassy in Tehran after revolutionary militants seized it in 1979” during the hostage crisis.
When he returned to the US with the books, however, the FBI determined the volumes were classified and seized them.
Luckily, Worthy was able to acquire another set of volumes and provided them to Washington Post reporter –and Archive founder– Scott Armstrong.
Subsequently, in January 1982 Armstrong published a five-part series, “Iran Documents Give Rare Glimpse of a CIA Enterprise,” about United States intelligence operations in Iran, based partly on the contents of the documents provided by Worthy.
In an interview with Democracy Now’s Amy Goodman, Scott Armstrong called Worthy’s documents “an extraordinary find.” He said:
“This was a whole history. I think there were—he brought back 12 of 13 volumes that existed then. Later, we ended up with 90 volumes in all. But it was an extraordinary insight into the history of overthrowing Mosaddegh, the popularly elected leader of Iran; re-installing the Shah, the CIA’s role in that; and then the cooperation that the CIA gave with SAVAK, the dreaded secret police of Iran. And it was—every intimate detail was included. They just—they had some documents in their entirety that just hadn’t even gotten to the shredder and other things that they were able to print out that were still in electronic form, that showed the U.S. government reaction to pressure on the Shah as the revolution occurred in Iran. And the United States did not deal with itself well. The United States government at one point during the hostage crisis considered releasing these documents, and Cy Vance advocated it, but it chose instead to try a military rescue. So, these documents were—essentially put a lie to every defense that had been given for the U.S. role in Iran over a 30- or 40-year period at that point.”
Armstrong was careful to note in his 1982 expose that, while the volumes provided an unprecedented glimpse of the CIA’s activities, not all of the documents that were found in the US Embassy in Tehran had been deciphered, and others had but were ultimately withheld because they “might embarrass Islamic clerics the militants support.” Armstrong noted that while the published documents did not support some of the militants more “egregious” conspiracy theories about the US’ activities in Iran, the documents were “used in an intensive campaign to arouse further distrust of the United States.”
For its role in attempting to suppress the dissemination of Worthy’s volumes and tighten the lid on the US government’s activity in Iran, the FBI agreed to pay $16,000 to settle a suit brought by Mr. Worthy, his colleagues, and the American Civil Liberties Union over the volumes’ seizure.
In his interview with Goodman, Armstrong also elaborated on how Worthy’s collection convinced him and others to establish the National Security Archive.
“These documents were so complete and, once authenticated, painted such an unusually detailed picture of the U.S. machinations in Iran, that it became apparent that there was always going to be an understory, there was always going to be something in the background that journalists suspected, but were often unable to write about, because, at that point, the Reagan administration was there. The Reagan administration was attempting to intimidate Bill Worthy, attempting to intimidate other journalists. A year after I wrote the series, they came down with a National Security Decision Directive 84, which was—which said that no person in the United States government could talk to a member of the press about anything involving national security without first clearing it with the National Security Council. And that lasted about a week, because there was such an uproar from the press. But we were—it was still unclear whether the press was really going to pursue things like the Iran-Contra activities that were beginning to go on. The war in El Salvador had heated up again. And the Reagan administration was re-inventing facts every day of the week. And they would just make conclusory statements. They would deny things that were quite obvious to the journalists on the ground in different countries. And often our editors were intimidated.So the question became: Was it possible to put together large groups of documents, get them declassified or otherwise accumulate them, and keep them in the public domain? And we tried it with—actually, it was an ACLU project at—in Washington that dealt with the questions of asylum for Salvadorians. And both Ray Bonner from The New York Times and I had independently used the Freedom of Information Act to request things, and we’d gotten back different—the same documents. Often, Ray would get back one where the top half was excluded and the bottom half was there, under national security grounds; I’d get back the same document, the top half included and the bottom excluded. So we began to put these things together, and we began to see that there were ways to get an authenticated version of what actually happened on the ground that would at least begin to pin down the administration on what its policy had been. I mean, documents do lie, in the sense that we are talking about communications between policymakers who have their own point of view, but they at least have the authenticity of showing what those points of view were and allowing people—allowing journalists to say something definitive about the position of the United States government at a particular point in time.And it was that notion that we could do this, we could do something that was across the board on many different topics, that caused the National Security Archive to be created. It was one of the unintended consequences, I guess, of Bill Worthy’s exercise of his right to travel and his right to read and think and do what he wanted as a journalist. We began to exploit that right. And the Bill of Rights exists only insofar as you exercise it. So I left—at one point, left The Washington Post and founded the National Security Archive.”
Key selections of the volumes Worthy gave to Scott Armstrong were published electronically in the Archive’s second digital collection, Iran: The Making of U.S. Policy, 1977-1980, and are currently housed in the Archive’s conference room.
Today the Department of Justice Office of Information Policy (OIP) is beginning its review process to determine the potential content of “a core FOIA regulation and common set of practices” to be used across the government. Noting OIP’s less-than-sterling FOIA track record, Archive FOIA Coordinator Nate Jones has warned, “Vigilance is required by the requester community to ensure that the Common Regulation actually does lead to the release of more documents, more quickly.” To help ensure that these core FOIA regulations help standardize disparate, and often outdated, FOIA processes along best practice guidelines, the Archive, along with our colleagues at the Citizens for Responsibility and Ethics in Washington (CREW), and the Electronic Privacy Information Center (EPIC), recently published our set of model FOIA regulations, which will be the “standard against which the results of the administration’s review will be judged.”
The White House announced Tuesday that it will examine how the name of the CIA’s top officer in Afghanistan, the Chief of Station in Kabul, was inadvertently released by the White House press office to thousands of reporters. The CIA officer, who works undercover, was included on a listprovided to news organizations “of senior U.S. officials participating in President Obama’s surprise visit with U.S. troops” at Bagram air base outside of Kabul, Afghanistan. The embarrassing slip comes at the same time the Obama administration announced plans to reduce troop levels in Afghanistan and end combat operations there by the end of the year.
Earlier this week, Attorney General Eric Holder hinted that the government might not pursue jailing New York Times reporter James Risen for refusing to testify in a leaks trial, all the while pursuing the administration’s right to do so. Risen was subpoenaed to testify in former CIA official Jeffrey Sterling’s leaks trial resulting from his disclosures to Risen regarding Operation Merlin, “a Clinton-era effort by the C.I.A. to sabotage Iranian nuclear research by sending a Russian scientist to sell flawed blueprints to Iran,” which were the subject of a chapter in Risen’s 2006 book, State of War. While meeting with a group of journalists to discuss press freedoms, Mr. Holder said, “As long as I’m attorney general, no reporter who is doing his job is going to go to jail. As long as I’m attorney general, someone who is doing their job is not going to get prosecuted.”
Hector Monsegur, known online as Sabu, a prominent hacker and leading figure in both Anonymous and its splinter group LulzSec,was released from prison after federal judge Loretta Preska praised his “extraordinary cooperation” with the FBI. While the US government calculates Monsegur participated in over 250 hacking attacks that cost $50 million in damages, he received a lenient sentence thanks to his willingness to help “identify and convict eight of his peers in the Anonymous and LulzSec hacker collectives. Most notably, he was seminal in nailing Jeremy Hammond, who at the time was the FBI’s number one most wanted cybercriminal in the world, for his role in hacking into the private intelligence firm Stratfor.” Hammond, now serving a ten-year sentence, argued that Monsegur had directed much of Hammond’s activity, and “had supplied him with lists of foreign countries vulnerable to attack including Brazil, Iran and Turkey. Hammand went so far as to suggest that the FBI had been using him to launch cyber-attacks around the world, with Monsegur acting as the coordinator.”
Freedom of Information Act (FOIA) requests garnered the release of 4,000 pages of unclassified emails and reports on efforts to monitor the Occupy movement in 2011 and 2012. The Occupy information was collected and disseminated by the US’ 78 counterterrorism intelligence-sharing offices, known as fusion centers, and the released information highlights their often disparate approaches to monitoring activity. While some centers distanced themselves from monitoring Occupy, others monitored “apparently lawful, even routine activities.”
WikiLeaks recently released a statement saying that Country X, a country whose identity has yet to be officially confirmed and whose full audio content the National Security Agency (NSA) monitors as part of Operation MYSTIC, is Afghanistan. The Intercept recently revealed that the NSA is “secretly intercepting, recording, and archiving the audio of virtually every cell phone conversation on the island nation of the Bahamas” and one other country, which it did not name. WikiLeaks released its statement naming that country as Afghanistan because it could not “be complicit in the censorship of victim state X.”
U.S. District Court Judge Gladys Kessler ruled that the US military can force-feed Abi Wa’el Dhiab, a Syrian detainee being held at Guantanamo Bay, to prevent him from dying. She urged the Department of Defense, however, “to consider alternative methods” to keep him alive, saying that the Pentagon’s “intransigence” or refusal to compromise meant that “Mr. Dhiab may well suffer unnecessary pain from certain enteral feeding practices and forcible cell extractions. However, the Court simply cannot let Mr. Dhiab die.” Kessler additionally ordered the government to release 34 videos of the force-feedings to Dihab’s lawyers by June 13th.
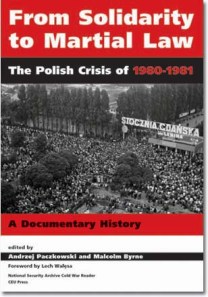
Gen. Wojciech Jaruzelski, the Polish leader who declared martial law in 1981 to crush the Solidaritymovement, died this week at age 90. The Archive’s 2006 book, From Solidarity to Martial Law: The Polish Crisis of 1980 – 1981, provides a documentary history of Solidarity, the Polish communist party leadership, the Kremlin, the White House, and the CIA, during one of the most dramatic episodes in the Cold War.
The Archive commends the long-awaited release of the State Department’s Foreign Relations of the United States (FRUS) volume XXI, Chile: 1969-1973, in a recent posting. The FRUS volume addresses Richard Nixon’s and Henry Kissinger’s efforts to destabilize the democratically elected Socialist government of Salvador Allende, and the U.S.-supported coup that brought General Augusto Pinochet to power in 1973.
The Archive’s latest posting provides excerpts from Anatoly S. Chernyaev’s 1974 diary, published in English for the first time. Chernyaev was the deputy head of the International Department of the Central Committee (and later the senior foreign policy aide to Mikhail Gorbachev), and he started keeping a systematic diary in 1972 that recorded the highs and lows of his work at the International Department, his attendance at Politburo meetings, philosophical reflections on daily life in the Soviet Union, and more. This is the ninth set of extracts the Archive has posted covering selected critical years from the 1970s through 1991.
Finally this week, our #tbt document pick! This week’s pick comes from our 2006 posting,Solidarity and Martial Law in Poland: 25 Years Later. It is Lt. Gen. Viktor Anoshkin’sDecember 11, 1981, notebook entry, which provides “one of the more important pieces of evidence to emerge in recent years concerning Jaruzelski’s desire for Soviet military assistance in connection with martial law.”
Happy FOIA-ing!

Aerial view of the ranch just outside the town of San Fernando, Tamaulipas, where the bodies of 72 murdered migrants were discovered in August 2010.
Judge Rules Mexican government must disclose evidence of grave human rights violations
Migrant killings in Tamaulipas, Cadereyta, prima facie human rights violations
Landmark decision upholds right to truth, cites “interest of society” in “avoiding impunity and the repetition of such acts in the future”
Can the Mexican government continue to hide evidence from the public about grave human rights atrocities? A pair of access to information cases now moving through the Mexican justice system may put an end to the practice.
In a landmark decision in support of the right to the truth, a Mexican federal judge for the first time has ruled that three horrific migrant massacres from 2010-2012 constitute clear violations of human rights and said the Attorney General’s office (Procuraduría General de la República-PGR) is required to release a public version of its investigatory files on the cases. The investigations have long been shrouded in secrecy amid charges that state agents in some cases may have collaborated with the criminal groups responsible for the killings.
The cases stem from a shocking series of mass murders in northeastern Mexico that took the lives of hundreds of migrants. The victims, mainly Central Americans kidnapped from intercity buses while traveling north to the U.S.-Mexico border, were pawns in a brutal conflict between criminal organizations, who murdered them with impunity, in some cases simply to prevent them from falling into the hands of their rivals. In one case, the corpses of 49 victims were completely dismembered before being dumped along the side of the road in the town of Cadereyta Jiménez, Nuevo León, making identification of the corpses especially difficult.
The ruling comes in response to an access to information request brought by Mexico’s Fundación para la Justicia y el Estado Democrático de Derecho (FJEDD) on behalf of the families of victims from those cases.
The court’s decision is a crucial breakthrough for efforts to obtain official information on gross abuses against migrants in Mexico and the latest in a growing body of important legal precedents in Latin America affirming the right to information as a fundamental human right. Migrant victims, their family members, and broader society have the right to know the truth behind such acts of violence, according to the 60-page decision.
“Avoiding impunity and the repetition of such acts in the future”
The Mexican attorney general’s office had refused to divulge the files under Mexico’s freedom of information law citing exemptions in Article 14 (I) and (II) of the Transparency Law, and Article 16 of the Federal Code of Criminal Procedure, allowing the government to withhold information related to “averiguación previa” (“preliminary investigation”). But that exception, the judge asserted, is in these cases trumped by the last paragraph of Article 14 of the Federal Transparency Law, which says that the government can in no case withhold information about grave human rights violations and crimes against humanity. (See Article 14, final paragraph of Mexico’s Transparency Law)
Citing international court decisions, United Nations declarations, and the Mexican Constitution, Judge Fernando Silva García said transparency in such cases is key to “avoiding impunity and the repetition of such acts in the future.” The sensitive nature of investigatory files is precisely why it is so important to make them public, since they “affect society as a whole.” Mexico’s access law, he wrote,
… foresaw an exception to withholding files on preliminary investigations in those extreme cases in which the crime being prosecuted is of such gravity that the public interest in maintaining the preliminary investigation files in secrecy is superseded by the interest of society as a whole in knowing of all the actions that are being brought to bear for the timely investigation, detention, judgment and sanctioning of those responsible.
State complicity
Key to Judge Silva García’s determination that the cases qualified as a grave violations of human rights is the abundance of evidence that state officials may be connected to the murders. State participation or acquiescence in the act is one of three criteria required to establish that violations are grave abuses under guidelines established by the Inter-American Court of Human Rights and approved by the Mexican Supreme Court.
His decision cites multiple authorities, including the United Nations and Mexico’s National Human Rights Commission (CNDH), which have found evidence of Mexican officials’ complicity in targeted abuses against migrants, particularly in the wave of kidnappings and murders that overtook the states of Tamaulipas and Nuevo León during those dark years. Other reports cited the state’s failure during that time to take the steps necessary to prevent further abductions.
Declassified documents obtained by our organization and shared with the plaintiffs in this case underscore charges that state officials collaborated in migrant abuses. One U.S. Embassy cable highlights the arrest of 16 police officials in connection to the 2010 massacre of 72 migrants in San Fernando, Tamaulipas, and the fact that state officials were “trying to downplay both the San Fernando discoveries [of mass graves] and the states [sic] responsibility for them.” Embassy officials said they did so despite being “fully cognizant of the hazards of highway travel in this area.” Another U.S. report described a state of “near total impunity” for criminal organizations operating in that region “in the face of compromised local security forces.” (See previous post on U.S. documents on San Fernando massacre).
While a number of people have been arrested in relation to the crimes, there has been little information available on the cases against them. The presumed authors of the violence, Édgar Huerta Montiel (“El Wache”) and Martín Omar Estrada Luna (“El Kilo”) remain in detention. Miguel Ángel Treviño Morales, the top leader of the Zetas, was arrested by Mexican authorities in July 2013. More recently, Mexico reported the arrest of an alleged human smuggler (pollero) said to be linked to the case.
Information commissioners violated rights of victims
In denying the information, Mexico’s attorney general argued that none of the massacres had been identified as human rights violations by a competent legal authority. Mexico’s Federal Institute of Access to Information (Instituto Federal de Acceso a la Información y Protección de Datos - IFAI), the appellate body for access to information cases in Mexico, also declined to make such a determination, declaring itself incompetent to do so.
But Judge Silva cast those arguments aside, ruling that the massacres were, prima facie, human rights abuses and that IFAI must order the Attorney General’s office to release a public version of its investigative files. The court also found that the IFAI commissioners are obliged to make such determinations for purposes of access to information; that IFAI should no longer allow agencies to deny access to judicial files when they pertain to human rights crimes; and, perhaps most importantly, that IFAI had violated the rights of the victims and their families in denying access to the information in the first instance.
“[I]f IFAI has any doubts with respect to [this ruling],” Judge Silva wrote, “the authorities should be governed by the principles of good faith, of maximum disclosure, and as the Inter-American Court of Human Rights signaled in the case of Gomes Lund vs Brasil with respect to grave violations of human rights: ‘when in doubt or in the case of a legal vacuum, the right of access to information should take precedent.’”
Test case for new information commissioners
This and a similar case brought by the pro-transparency group Article 19 shine a spotlight on IFAI just as the oversight body is undergoing a major transformation in personnel and responsibilities. The rulings have forced a newly-selected group of IFAI information commissioners to make a clear statement on human rights and access to information during their first weeks in office. Unfortunately, IFAI elected to join the PGR in appealing the judge’s ruling, further delaying the release of important information on these important cases to victims, their families and members of the public.
Still, Judge Silva’s passionate defense of the right to truth offers a clear legal path for Mexico to overcome such challenges and abide by both the letter and the spirit of the Mexican access law and a growing body of international jurisprudence guaranteeing access to information on grave human rights abuses.
Model FOIA Regulations
MAY 22, 2014

The latest Archive audit highlighted just how outdated many agency FOIA regs are.http://www2.gwu.edu/~nsarchiv/NSAEBB/NSAEBB460/
The National Security Archive has partnered with our colleagues at theCitizens for Responsibility and Ethics in Washington (CREW), and the Electronic Privacy Information Center (EPIC), to publish a set of model Freedom of Information Act (FOIA) regulations. These model regulations will set the transparency benchmark when the Department of Justice’s Office of Information Policy begins the review process to determine the potential content of “a core FOIA regulation and common set of practices” to be used across the government on May 29th.
While FOIA regulations are the principal tool agencies use to process their FOIA requests, nearly half (50 out of 101) of all federal agencies have not updated their FOIA regulations to comply with Congress’s 2007 FOIA amendments, many regulations are difficult to find, and FOIA processes differ greatly across the 101 federal agencies, “making it difficult for information-seekers to navigate red tape.”
The model FOIA regulations drafted by CREW, EPIC, and the Archive, will help standardize these disparate, and often outdated, FOIA processes along best practice guidelines.
CREW’s policy director, Daniel Schuman, has a great post on the newly-published model regulations, which include:
o Protecting media access by treating an online-only news organization as a “representative of the news media” and thereby qualifying for a FOIA fee waiver.
o Saving taxpayer resources by encouraging agencies to post documents released through the FOIA process online.
o Providing agencies with a concrete process for applying the oft-abused “pre-decisional” Exemption 5 by including a public interest balancing test and limiting the exemption’s use to documents created less than 12 years ago.
o Making disclosure the default by formalizing the president’s directive for an agency to release information in response to a request except when the agency clearly identifies specific, foreseeable harm arising from the disclosure.
o Reducing unnecessary secrecy by requiring agencies to review classified documents that are the subject of a FOIA request to see whether they now can be disclosed.
o Ending the paper chase by allowing agencies to avoid unnecessary consultations through the use of inter-agency agreements.
o Managing expectations around FOIA appeals by setting a uniform 60-day deadline.
o Encouraging dispute mediation by informing the public that the Office of Government Information Services can help settle disputes.
o Reducing disputes over fees by clarifying several issues.
o Applying the law on fees so agencies do what Congress intended.
Take a look at the complete model regulations here.
In a split ruling that exposes the gap between Obama’s transparency promises and actual bureaucratic (and judicial) behavior, the US Court of Appeals for the DC Circuit ruled this week that the final 30-year-old volume of the CIA’s draft “official history” of the Bay of Pigs invasion could be withheld from the public under the b-5 “deliberative process” exemption, even though four of the five volumes have previously been released with no harm either to national security or any government deliberation. The National Security Archive’s Cuba project director, Peter Kornbluh, requested all five volumes through the FOIA on the 50th anniversary of the Bay of Pigs invasion in 2011, eventually filing suit for the fifth and final volume in 2012. Prior to this week’s decision, the Obama administration bragged that reducing the government’s invocation of the b-5 exemption was proof of the impact of the President’s Day One commitment to a “presumption of disclosure.” Instead, the bureaucracy has actually increased its use of the b-5 exemption in the last two years, which current White House counselor John Podesta once characterized as the “withhold if you want to” exemption.
The Department of Defense recently admitted it has video recordings of force-feeding Guantanamo Bay detainees. The news comes at the same time detainees are accusing the US of manipulating data on inmates’ hunger strikes, including how many times inmates are subjected to force feedings to keep strike numbers artificially low. A lawyer for one of the detainees, Abi Wa’el Dhiab, submitted court filings to preserve the force-feeding tapes, in large part because in 2005 “the CIA destroyed nearly 100 videotapes of interrogations of detainees in its custody.” The court ordered the government to turn over the 34 videotapes yesterday.
The Obama administration delivered a nine-page unclassified report to Congress last week expressing confidence that “if Guantánamo Bay detainees were relocated to a prison inside the United States, it is unlikely that a court would order their release onto domestic soil.” Congress requested the report in last year’s National Defense Authorization Act after it prohibited the president’s previous plan to send detainees “too difficult to prosecute but too dangerous to release” to high-security prisons in Standish, Mich., or Thomson, Ill.

President Obama and Uruguay President Jose Mujica speak to the press before a meeting in the Oval Office of the White House May 12, 2014. Brendan Smialowski/AFP/Getty Images
President José Mujica of Uruguay said his country would accept six Guantanamo detainees –those “cleared for release but can’t return to their nations, either because of war, fear of torture or security concerns about their home countries”– with the caveat that the US must accept his offer before he leaves office early next year. Mujica, who spent thirteen years in prison during the ‘60s and ‘70s for guerilla activities against Uruguay’s military dictatorship, said “the prisoners will be considered normal refugees, and that his government does not intend to monitor them.”
According to documents leaked by former contractor Edward Snowden, the National Security Agency (NSA) is “secretly intercepting, recording, and archiving the audio of virtually every cell phone conversation on the island nation of the Bahamas.” The surveillance is part of the NSA’s SOMALGET program, a subsection of its MYSTIC program, and was implemented without the knowledge of the Bahamian government. SOMALGET records, stores, and can replay the “full-take audio” of every phone call made to, from, or within the island for up to a month. According to a Department of State crime and safety report published last year, “[t]he Bahamas is a stable democracy that shares democratic principles, personal freedoms, and rule of law with the United States There is little to no threat facing Americans from domestic (Bahamian) terrorism, war, or civil unrest.”
Language in the finalized USA Freedom Act, poised to be voted on in the House shortly, would require the government to “promptly” purge phone records that don’t contain any foreign intelligence information. The previous language required the government to destroy such information after five years. Several other changes to the bill, however, have cost it the support of many privacy advocates and civil libertarians, who say the bill has been “gutted,” particularly by “the Intelligence Committee, who supported the NSA phone records program.” Technology companies, including Facebook, Google, Apple, Microsoft, and Yahoo, have also pulled their support from the bill, saying the legislation “moved in the wrong direction” after House Republicans privately negotiated with President Obama’s administration “to alter the legislation.”
The Obama administration announced that the CIA is no longer using immunization programs as a front for spying. The announcement was delivered to a group of American health educators three years after the CIA fronted a fake hepatitis vaccination program in Pakistan in a failed attempt to nab Osama bin Laden. “Dozens of public health workers in Pakistan have been killed, with militant groups sometimes announcing that the workers had been suspected of being spies,” since the CIA program first became public.
The US charged members of Unit 61398, China’s cyberwarfare unit, with economic espionage in a move that signifies the administration’s belief “that there is a major difference between spying for national security purposes” and for-profit espionage. The indictment, released by Attorney General Eric Holder, “included allegations that Unit 61398 had stolen trade secrets for nuclear power plants that would save Chinese firms years of design work, as well as information from inside an American solar energy company that was pursuing a trade complaint against its Chinese competitors.” The timing of the indictment is somewhat curious, given documents recently leaked by Snowden reveal that the NSA spied on Brazil’s oil giant, Petrobras, and hacked into the computer systems of China Telecom.
The Justice Department will release the secret 2011 memo justifying drone strikes against American citizens in a “matter of weeks.” The announcement was made “on the eve of a Senate vote on President Obama’s nomination of David J. Barron, one of the memo’s authors, to a federal appeals court judgeship” after liberal and conservative senators promised to fight his nomination if the memo wasn’t made public. This announcement comes two and a half years after the Department of Justice Office of Legal Counsel told the National Security Archive that it “neither confirms nor denies the existence of” the memorandum authorizing the lethal targeting of Anwar al-Awlaki, and the Second Circuit Court of Appeals’ unanimous rejection of the DOJ’s claims for refusing to review the memo for release to the New York Times and the American Civil Liberties Union.
Sen. John McCain (R-AZ) plans to introduce language into the Senate Armed Services Committee’s version of the 2015 National Defense Authorization Act that would give the Defense Department control over the drone program, currently controlled by the CIA, arguing that the move would increase transparency. In response to the news, Senate Intelligence Committee chairwoman Dianne Feinstein (D-CA) said, “[t]he intelligence people are really experts at [drone strikes]. The military really isn’t.”

Rwandan Patriotic Front (RPF) soldiers in Rwanda, circa September 1994. Photo from personal collection of Prudence Bushnell.
For the seventh posting in our joint effort to mark the 20th anniversary of the Rwandan genocide, Archivist Emily Willard examines the failure of the Arusha Peace Accords and chronicles the international community’s role in the failure to implement the demobilization program, a key part of the Accords, ultimately leading to genocide in April 1994. Read Willard’s analysis and the newly posted documents here.
Finally, in light of the DC Circuit Court of Appeals’ decision to sanction the CIA’s refusal to disclose the fifth volume of its five-volume official history of the Bay of Pigs invasion, this week’s #tbt document pick is a 2011 posting on the first four volumes of that official history. In 2011, the National Security Archive’s Cuba project director, Peter Kornbluh, postedsome of the biggest revelations from the first four volumes, released to the Archive in response to a FOIA request that year, including episodes of CIA “friendly fire” during the invasion, a discussion of using napalm bombs against the Castro regime, a plot to involve the Mafia in an attempt to assassinate Castro, and much more. Check out the first four volumes of the Bay of Pigs history on the Archive’s website.
Happy FOIA-ing!
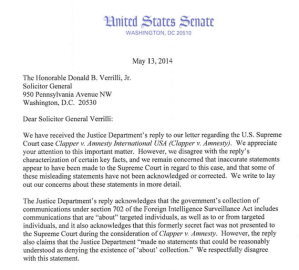 Senators Mark Udall (D-CO) and Ron Wyden (D-OR) sent a letter to Solicitor General Donald B. Verrilli criticizing him and the Department of Justice for its misleading statements about the National Security Agency’s (NSA) warrantless surveillance practices before the Supreme Court in 2013. In their letter, the senators accused the White House of attempting to “ignore or justify” the DOJ’s statements, and contributing to a “culture of misinformation” by the executive branch regarding its surveillance programs.
Senators Mark Udall (D-CO) and Ron Wyden (D-OR) sent a letter to Solicitor General Donald B. Verrilli criticizing him and the Department of Justice for its misleading statements about the National Security Agency’s (NSA) warrantless surveillance practices before the Supreme Court in 2013. In their letter, the senators accused the White House of attempting to “ignore or justify” the DOJ’s statements, and contributing to a “culture of misinformation” by the executive branch regarding its surveillance programs.
Solicitor General Verrilli made the misleading statements before the Supreme Court in 2013 during the Clapper v. Amnesty International case. During the case, Verrilli erroneously argued that defendants were notified whenever information used against them was obtained pursuant to Section 702 of the FISA Amendments Act of 2008. While the DOJ is now –belatedly– informing defendants when evidence used against them was obtained by warrantless surveillance, it wasn’t doing so at the time of the Clapper case. Verrilli also argued that Section 702 surveillance was done directly on foreign suspects, whereas it was actually interpreted by the NSA to allow the inclusion of wholly-domestic communications when a foreign suspect’s identifier, such as an email address, was mentioned in a communication.
Documents recently posted to the Office of the Director of National Intelligence’s website reveal that in 2010 Sprint was shown the secret legal basis for the NSA’s dragnet domestic surveillance practices. Sprint was shown the information after threatening to file a court challenge over the NSA’s request for its records, and was the only telecommunications company to demand –or receive– the program’s legal underpinnings. “But after being shown the documents, the company dropped its challenge and continued to turn over customers’ call-detail records to the NSA.”

NSA head Adm. Mike Rogers promises to make his agency more transparent. Photo: Reuters/Larry Downing
Steven Aftergood of the Federation of American Scientists recently reported that the Office of the Director of National Intelligence is now requiring all employees and contractors to obtain “authorization before disclosing any intelligence-related information to the public.” This new directive pertains to information that is classified and unclassified and applies broadly to any information generated by ODNI “that discusses operations, business practices, or information related to the ODNI, the IC, or national security.” ODNI responded by saying “[r]ecent media reports have misconstrued ODNI’s policy for pre-publication of information to be publicly released,” arguing that its new policy is not significantly different from previous ones, a claim that is hard to swallow considering none of the previous policies applied to unclassified information. Meanwhile, Adm. Mike Rogers said in his first interview since taking control of the NSA that he vowed to “lead the embattled spy agency with greater transparency as it balances individual rights against the rising risk of a destructive cyber attack against the United States.”
The Guardian, via documents leaked by Edward Snowden and described in Glenn Greenwald’s book No Place to Hide, reported that the NSA allegedly tampers with US-made computer hardware before re-packaging and shipping the products overseas. In his book, Greenwald refers to a June 2010 report that outlines the NSA’s practice of “intercepting US-made hardware, embedding backdoor surveillance tools, then repackaging the equipment and sending it onto international customers,” –a practice the US recently accused Chinese telecom giant Huawei of, eventually forcing the company out of the US market.
The Washington Post revealed that members of the elite Secret Service unit Prowler, which is tasked with patrolling the White House, were ordered by the agency director to abandon their post to watch his personal friend for two months in 2011. The detail, known as Operation Moonlight, sent the agents to a Maryland suburb, nearly an hour’s drive from the White House. The agents involved were concerned about the legality of their re-assignment, and some reported the issue to the Secret Service’s parent agency, the Department of Homeland Security. According to the Post, “[p]eople familiar with the operation said a Senate committee’s recent findingthat the former DHS inspector general softened and delayed investigations — particularly those critical of administration officials — renewed frustration that the issue may have not been properly investigated.”
The debate surrounding whether or not to transfer control of the CIA’s lethal drone program to the Pentagon intensified this week. McClatchy DCreported that in the wake of a Pentagon-led drone attack that killed a dozen Yemeni civilians last December, an attack that was based on intelligence the CIA later called questionable, some members of Congress believe the Pentagon and the Joint Special Operations Command are “not as careful as the CIA, and shouldn’t be given responsibility for drone killings.” This February, Director of National Intelligence James Clapper publicly acknowledged the existence of the CIA drone program for the first time in a Senate Armed Services Committee hearing, during which Sen. Bill Nelson (D-FL) asked Clapper to confirm if the White House was considering “shifting the use of drones, unmanned aerial vehicle strikes, from the CIA to the DOD,” to which Clapper responded, “Yes, sir, it is. And again, that would also be best left to a closed session.” Congress, however, had already “secretly slipp[ed] language into the omnibus spending bill that preserves the CIA’s role in lethal counterterrorism operations,” restricting the Obama administrations ability to transfer the program to the Pentagon.
The New York Police Department recently shut down its controversial Demographics Unit, which came under intense scrutiny for spying on Muslim neighborhoods and designating entire mosques “terrorism enterprises.” The NYPD’s Citywide Debriefing Team, however, still scoursNYC jails looking for predominately Muslim immigrants to recruit as potential informants, demonstrating “that the department has not backed away from other counterterrorism initiatives that it created in the years after the Sept. 11 attacks.”
The Archive’s latest web posting examines the fascinating story behind the 1979 publication of Kermit Roosevelt’s book, Countercoup: The Struggle for the Control of Iran, which was delayed by threats from British Petroleum and the Iran Hostage Crisis. Internal CIA deliberations released through the FOIA and provided to the Archive by the original requester reveal Roosevelt agreed to delete all mention of MI6 from the book and made over 150 other changes that rendered it “essentially a work of fiction.” Visit the Archive to read the strange odyssey of Roosevelt’s book.
Be sure to check out Washington Free Beacon reporter C.J. Ciaramella’s first FOIA Rundown, the first installment from his new weekly newsletter on FOIA policy and transparency issues. The Archive is always excited to see reporters like C.J. dedicate their time and expertise to such important issues.

Boris Yeltsin in front of the Parliament on 08.19.1991 protesting the coup and Gorbachev’s house arrest.
Finally this week, the Archive’s #tbt document pick! This week’s pick is from a 2011 posting, The August 1991 Coup in Moscow, 20 Years Later, which examines the documents behind the coup that intended to topple Soviet president Mikhail Gorbachev but ultimately invigorated the Russian democratic opposition and sped up the collapse of the USSR. The #tbt document pick itself –atranscript from the August 21, 1991, First Extraordinary Session of the Supreme Soviet of the Russian Federation– brings the reader into the halls of the legendary Russian White House, to the extraordinary session of the Supreme Soviet of the Russian Federation at the exact moment of the triumph of the democratic resistance to the coup. Enjoy!
Happy FOIA-ing!
FRINFORMSUM 5/8/2014: Dueling House Surveillance Bills, NARA’s FOIA Advisory Committee, and Much More.
MAY 8, 2014
The House Judiciary Committee voted unanimously to advance a bill that would end the National Security Agency’s (NSA) dragnet collection of American’s phone records this week. The bill, the USA Freedom Act, is sponsored by Representative James Sensenbrenner (R-WI) and co-sponsored by 151 members of the House, and would authorize that bulk phone records stay with phone companies for the current 18-month requirement, and would only allow the government to obtain records of callers two links from a suspect, as opposed to the current three.
A rival bill from the House Intelligence Committee that also aims to end the NSA’s dragnet surveillance practices, co-sponsored by House Intelligence Committee chairman Representative Mike Rogers (R-MI) and ranking member C. A. Dutch Ruppersberger (D-MD), will likely be voted on today. The House Intelligence bill is a “somewhat less restrictive version of the [Judiciary] package,” and the primary difference between the two bills is the question of judicial review. Specifically, “a provision in the Judiciary bill [] would require a judge to approve records requests for each phone number before the NSA obtains them,” which the White House previously insisted be part of any new surveillance legislation. House aides predict that the USA Freedom Act will be the surveillance bill that advances to the Senate.
The National Archives and Records Administration (NARA) will create a FOIA advisory committee that will work to improve the way the government processes Freedom of Information Act requests. The creation of the FOIA advisory committee, which was announced in a May 5 Federal Register notice, comes nearly two months after the National Security Archive’s latest FOIA Audit reported that more than half of federal agencies still operate under obsolete FOIA guidelines.
A recent report by the American Immigration Council “found that 97 percent of abuse complaints lodged against Border Patrol agents and Customs and Border Protection (CBP) officers resulted in no disciplinary action once an investigation had been completed.” AIC’s report also found, thanks to a FOIA request, that complaints against Border Patrol agents and CBP “have more than doubled in size in the last seven years.” The most common abuses cites were physical abuse, excessive use of force, and racial profiling.
Corporations from Amazon to FedEx are putting pressure on the Federal Aviation Administration (FAA) to legalize commercial drone usage. Since 2007 the FAA has taken the position that commercial drones are illegal, even appealing an administrative order this April that “tossed out the legal foundation for its policy” declaring them so. The FAA, which has already approved over 600 public-sector entities to fly drones, plans to propose a rule for commercial drones by the end of the year.
Emails obtained by Al Jazeera in response to a FOIA request show that Google had a much closer relationship with the NSA than the company portrayed in the wake of Edward Snowden’s leaks about the agency’s surveillance practices. In one instance, the NSA “thwarted” a Chinese basic input/output system (BIOS) plot against the tech giant, arguing that the attack could have destroyed the US economy. Some, including Electronic Frontier Foundation attorney Nate Cardozo, argue it is contradictory for the NSA to help “Google secure its facilities from the Chinese and at the same time hack[] in through the back doors and tapping the fiber connections between Google base centers.”
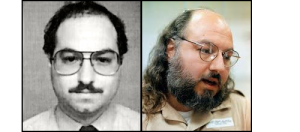
Jonathan Pollard: On the left is Pollards U.S. Naval intelligence I.D. photo, and on the right a 2012 photo of Pollard in prison.
The US will not allow Israeli citizens visa-free entry into the US over spying concerns. Israel has lobbied to add itself to the list of 38 countries the US currently allows visa exemptions for, however the US intelligence community has raised concerns over Israel’s espionage activities, which “greatly exceed that of any other American ally.” The White House is simultaneouslyconsidering releasing Jonathan Pollard, a former Navy intelligence analyst convicted of spying for Israel, to revive the floundering Middle East peace negotiations. Israel has petitioned successive presidents for Pollard’s release, with Clinton only dropping the idea after CIA director George Tenet threatened to resign if he did.
The Drug Enforcement Agency (DEA), while not acknowledging any wrongdoing, has agreed “to pay 14 contractors $500,000 to settle a lawsuit that accuses the agency of illegally requiring them to undergo highly intrusive lie detector tests to keep their jobs as translators.” Court documents show that during the polygraph tests, DEA employees asked the translators “very personal and even alarming questions about their lives, including about their sexual practices and crimes such as bestiality.” Polygraph testing also came under fire last months after the Inspector General for the Director of National Intelligence reported that federal agencies are inconsistent in reporting crimes divulged by potential employees during polygraph tests. The IG report attributed the inconsistencies, which occurred while testing at least 3 percent of personnel between 2009 and 2012, to “breakdowns in government reporting procedures and poor advice from agency lawyers.”
The New York Times reported this week that the long-secret “Midwest Depot,” an arms cache the CIA has used to stockpile and distribute “untraceable weapons linked to preparations for the Bay of Pigs invasion and the arming of rebels and resistance fighters from Angola to Nicaragua to Afghanistan,” is likely located at Camp Stanley, an Army weapons depot just north of San Antonio. The report credits retired CIA analyst Allen Thompson, who has “assembled a mosaic of documentation suggesting that it is most likely the home of Midwest Depot,” for the discovery.
Happy FOIA-ing!
The US must transition its analog FOIA practices to digital ones and fully embrace technology mandates to be a world transparency leader.
The US was the first country to enact a modern Freedom of Information Act, and was the model other countries looked towards when crafting their own FOI laws. Now, however, the US lags behind the world’s transparency leaders, and, if the US hopes to catch up, it must embrace the technology mandates of the 1996 E-FOIA Amendments and the 2007 OPEN Government Act. The best ways for the US to do this is by posting FOIA releases online, and convert its mostly analog FOIA process to a digital one.
Agencies are quick to argue why they don’t want to post FOIA releases online and why the practice wouldn’t work, and we have already dedicated a posting to rebutting these arguments, along with reasons why posting FOIA responses would not only work, but is imperative.
The point of today’s posting is to observe some of the world’s best practices. Countries like Mexico, the United Kingdom, Australia, and Norway all do a better job in some respects than the US when publishing public information electronically, and the US should incorporate and improve upon their best practices. If you know of any other examples of countries that have better FOI practices than the US currently does when it comes to posting FOI releases online, please leave them in the comments.
Mexico has one of the most sophisticated electronic FOI filing systems around. Through the system, called Infomex, a requester can search to see what’s already been requested and released across the Mexican federal government. If records responsive to an FOI request are in digitized form, they are uploaded to Infomex once they are released, and are available for public viewing and download. If records responsive to requests are not already digitized, however, they are generally not uploaded to the system, but Infomex still reports how the agency responded to the original request. The entire filing system is overseen by the Federal Institute for Access to Public Information (IFAI), which also handles appeals. While the Mexican filing system isn’t perfect, an obvious benefit if the US had a similar practice would be the elimination of cases where an agency releases a document in full after an initial FOIA request, only to release it with redactions in response to later ones.
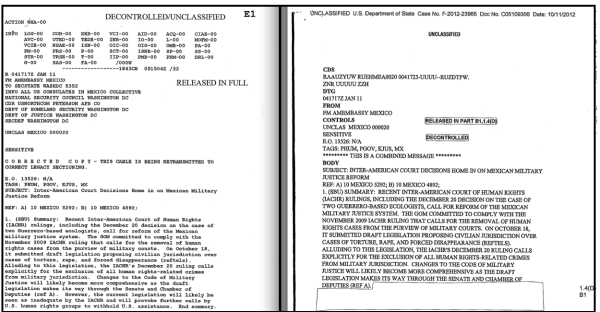
Take a look at the original, unredacted document, and the redacted version released a year later – by the same reviewer.
Similarly, while the UK’s FOI law has been the subject of heated debate, it does mandate the publication of its corporate FOI releases. Last September, the Wall Street Journal published an article on how US hedge funds and other commercial enterprises utilize the FOIA to “obtain potentially market-moving information about products, legislation, regulation and government economic statistics” in what the article described as an “information arms race.” Daniel Schuman of the Citizens for Responsibility and Ethics in Washington correctly notes that problems arise when the government doesn’t fulfill its legal obligation to publish these records after they have been requested. Currently, the US FOIA stipulates that “frequently requested” materials, which the Department of Justice defines as records that have been requested three or more times, must be posted by agencies somewhere in their electronic reading rooms. The FOIA additionally stipulates that agencies must “publish any record that has been released to any person and is likely to become the subject of additional requests.” As the Journal points out, responses to commercial requests fall into this category due to their ability to drive markets, impact the stock market, and ultimately what products become available to consumers. The US’ current practice of not releasing this desirable information manipulates markets by giving an unfair competitive advantage. To fix this, the US must begin posting commercial responses online as the FOIA mandates, and then fully fulfill the spirit of the FOIA by posting all responses online, period.
Amendments to Australia’s Freedom of Information Act that were enacted November 2010 “require agencies to publish information in a disclosure log within ten working days after the freedom of information (FOI) applicant was ‘given access’ to a document.” The disclosure logs are updated every Friday afternoon and cover, with some exceptions, requests from the previous week, and copies of the documents can be obtained via email requests. This practice of promptly posting FOI logs serves the public interest, and hasn’t, as some have worried, had an adverse impact on investigative journalists trying to get their exclusives. The E-FOIA Amendments of 1996 require US agencies to maintain and publish indexes of processed FOIA requests, though it does not specify how regularly these indexes or FOIA logs must be updated. Some agencies, however, like the Department of Homeland Security, have taken the initiative to post their FOIA logs online quarterly in order to provide the public an idea of what’s been requested, released, and who filed the request. The US should improve on Australia’s practices by not only requiring that all agencies post their FOIA release logs online regularly, but also requiring agencies to hyperlink to the responsive documents in their FOIA logs as well.
Norway’s Electronic Public Records (OEP) provision requires that federal agencies publisha daily register of metadata to an online access portal, which allows users to search all records across the government to make FOI requests. Currently, approximately 100 Norwegian government agencies use OEP to upload their public records, all doing so daily and according to a standard entry format, and these entries are then compiled into one common OEP database. While the OEP does not store the actual documents themselves, the single metadata repository includes the document’s case number, document title, sender/recipient information, exemption authorization, document date, and contact details for the authority responsible for the document. The US should improve on Norway’s OEP initiative not only by requiring agencies, either in a single repository or on an agency by agency basis, to regularly upload contact information that would make filing FOIA requests less cumbersome for requesters, but also by requiring agencies to regularly upload previous FOIA releases. This would not only boost the US’ transparency bona fides, but it would also save FOIA officers the trouble of processing multiple duplicate FOIA requests.
Of course, several agencies, including the and Department of State, Department of Defense Washington Headquarters Services, the Interagency Security Classification Appeals Panel, as well as the agencies participating in FOIAonline, already post documents online as they’re released. This is the direction the entire federal government should be heading. Not requiring all agencies to post documents online as they are released through the FOIA is a key misstep that is at odds with basic transparency principles of opening up government data for greater accountability, creates more work for both requesters and agency FOIA officers, costs more money, and leaves the United States in the second tier of Open Governments. The FOIA bill currently being drafted in the Senate is a prime opportunity to mandate that, aside from specific caveats including “first-party” requests made by requesters for documents about themselves and documents that are not already digitized, agencies’ default policies should be to post FOIA releases created after February 7, 2000, online. (The Section 508 Amendment to the Rehabilitation Act of 1973 specified that not later than February 7, 2000, all documents must be created digitally in formats accessible to people with disabilities.)
The United States was the first country to enact a modern Freedom of Information Act; it will return to the first tier of Open Governments only when it more fully enters the 21st century and begins making the documents it releases available online.